The Shifting Security Responsibility: Establishing a ‘Policy as Code’ Framework in Your CI/CD
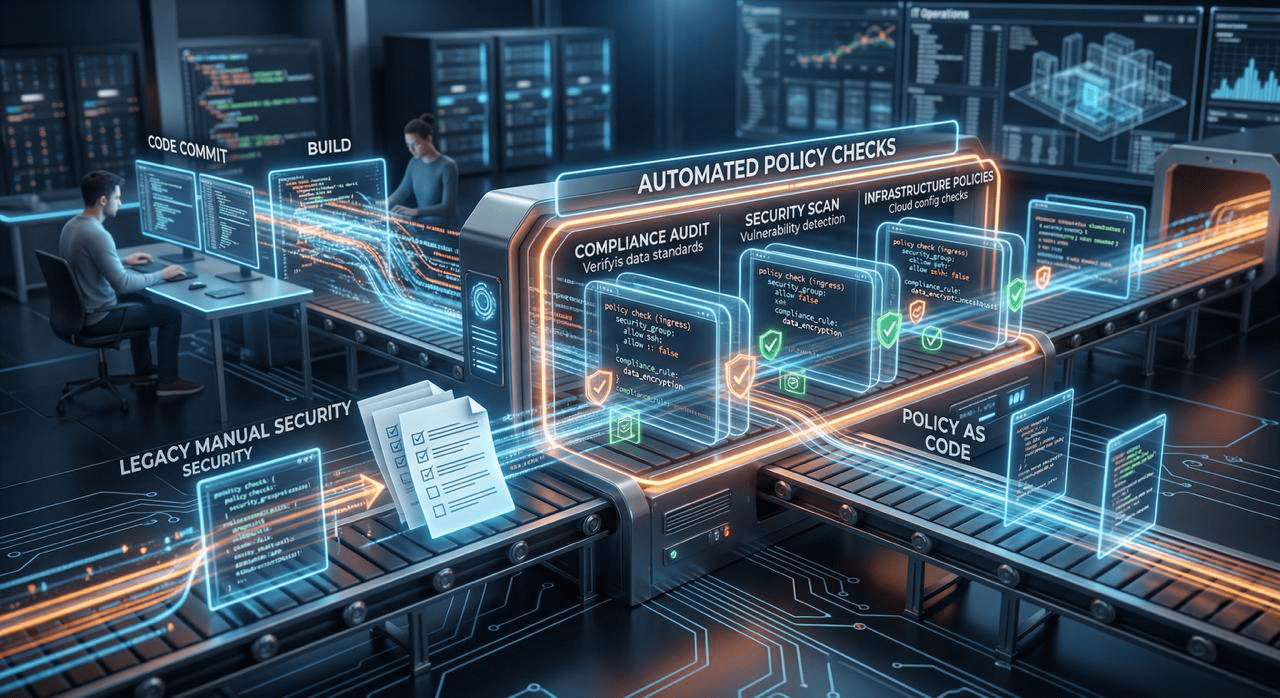
Modern software moves too fast for traditional manual security reviews. This post champions the DevSecOps philosophy, moving away from “find-and-fix” and toward automated prevention. We define Policy as Code (PaC) and introduce Open Policy Agent (OPA) as the industry standard tool.
The article provides concrete code examples showing how to write OPA policies (Rego language) that automatically check for common security flaws during the build phase—such as checking that Docker images don’t contain forbidden software packages, ensuring Kubernetes manifests restrict root access, or validating Terraform templates against security best practices (e.g., checking for public S3 buckets). The post demonstrates how to integrate these checks directly into pipelines (Jenkins, GitLab CI, GitHub Actions) as mandatory gatekeepers, ensuring that non-compliant infrastructure or code can never reach production.
